#indieauth
-
-
-
Dropping Twitter Support on IndieAuth.com
 I've made the difficult decision to drop support for Twitter authentication on IndieAuth.com. Some time last week, Twitter rolled out a change to the website which broke how IndieAuth.com verifies that a website and Twitter account belong to the same person.continue reading...
I've made the difficult decision to drop support for Twitter authentication on IndieAuth.com. Some time last week, Twitter rolled out a change to the website which broke how IndieAuth.com verifies that a website and Twitter account belong to the same person.continue reading... -
hosting Homebrew Website Club SF tonight @MozSF!
RSVP http://tantek.com/2018/080/e1
Special guest @aaronpk will demo his #IndieWeb reader setup!
https://aaronparecki.com/2018/03/12/17/building-an-indieweb-reader built on #openweb standards #WebSub #Microsub #microformats2 #IndieAuth #MicroPub #Webmention #Webhooks -
IndieAuth-Client-PHP 0.3.1
This release includes two new methods for quickly developing an IndieAuth client.continue reading... -
WebSub and IndieAuth Published on w3.org!
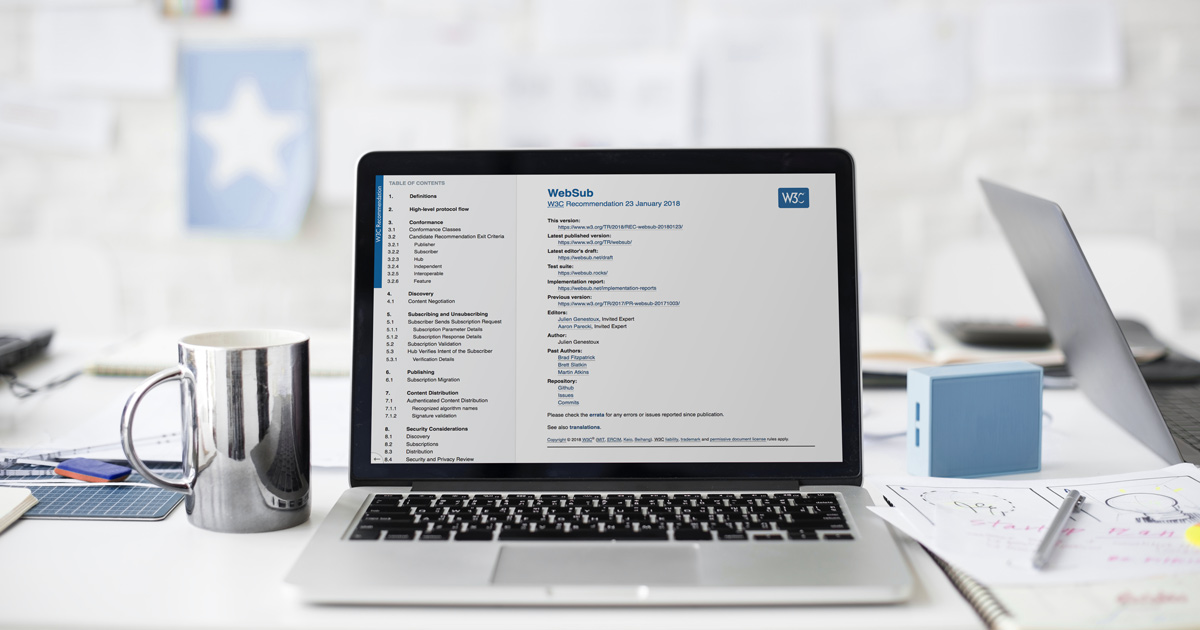 Today, we published the last of the two W3C specs I am editing! WebSub was published as a W3C Recommendation, and IndieAuth was published as a Working Group Note.continue reading...
Today, we published the last of the two W3C specs I am editing! WebSub was published as a W3C Recommendation, and IndieAuth was published as a Working Group Note.continue reading... -
-
Announcing the IndieAuth Spec!
It's been a long time coming, but I've finally published a proper IndieAuth spec!continue reading... -
-
#IndieAuth is SO MUCH easier than OAuth! https://indieauth.com/developers
No secret keys, etc, etc. Works against localhost! -
-
-
Day 86: Updating IndieAuth Docs #100DaysOfIndieWeb
Beginning a slow project of updating the docs about the IndieAuth spec, today I started by updating a few pages on the wiki. Right now, most of the docs about IndieAuth (the spec), and how to use it, live across a variety of pages on the wiki, grouped together at https://indieweb.org/Category:IndieAuth.continue reading... -
Day 81: Removing SMS and Clef from IndieAuth.com #100DaysOfIndieWeb
Sadly, Clef is shutting down in a couple months. If you haven't heard of it, it was a clever way to use your email and a mobile app to sign in to websites. I had integrated Clef logins to indieauth.com as one way to authenticate your email address. Since they are shutting down in June, I am proactively removing it from the website right now.continue reading... -
Day 73: Updated Documentation for indieauth.com #100DaysOfIndieWeb
Today I updated the documentation for indieauth.com to include a setup guide for using indieauth.com as your OpenID provider, and added more prominent links to the OpenID and PGP instructions in various places on the site.continue reading... -
-

