@aaronpk isn't the section you linked to just as much of a concern under the authorization code flow as the implicit flow? since javascript clients are public clients no matter what?
-
-
-
-
-
-
-
-
-
-
-
-
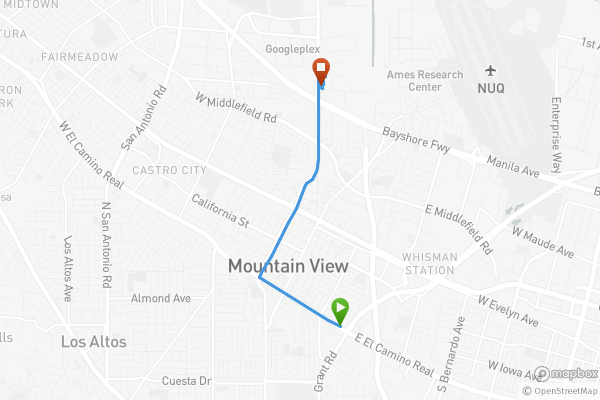
Mountain View, California • Thu, May 2, 2019 7:54am
-
-
at Hotel VueMountain View, California • Thu, May 2, 2019 7:29am
-
-
-
AsleepAwake8h 03mSlept23mAwake for